Cybersecurity Threats in Remote Work: How to Secure Your Virtual Office
Cybersecurity Threats in Remote Work: How to Secure Your Virtual Office
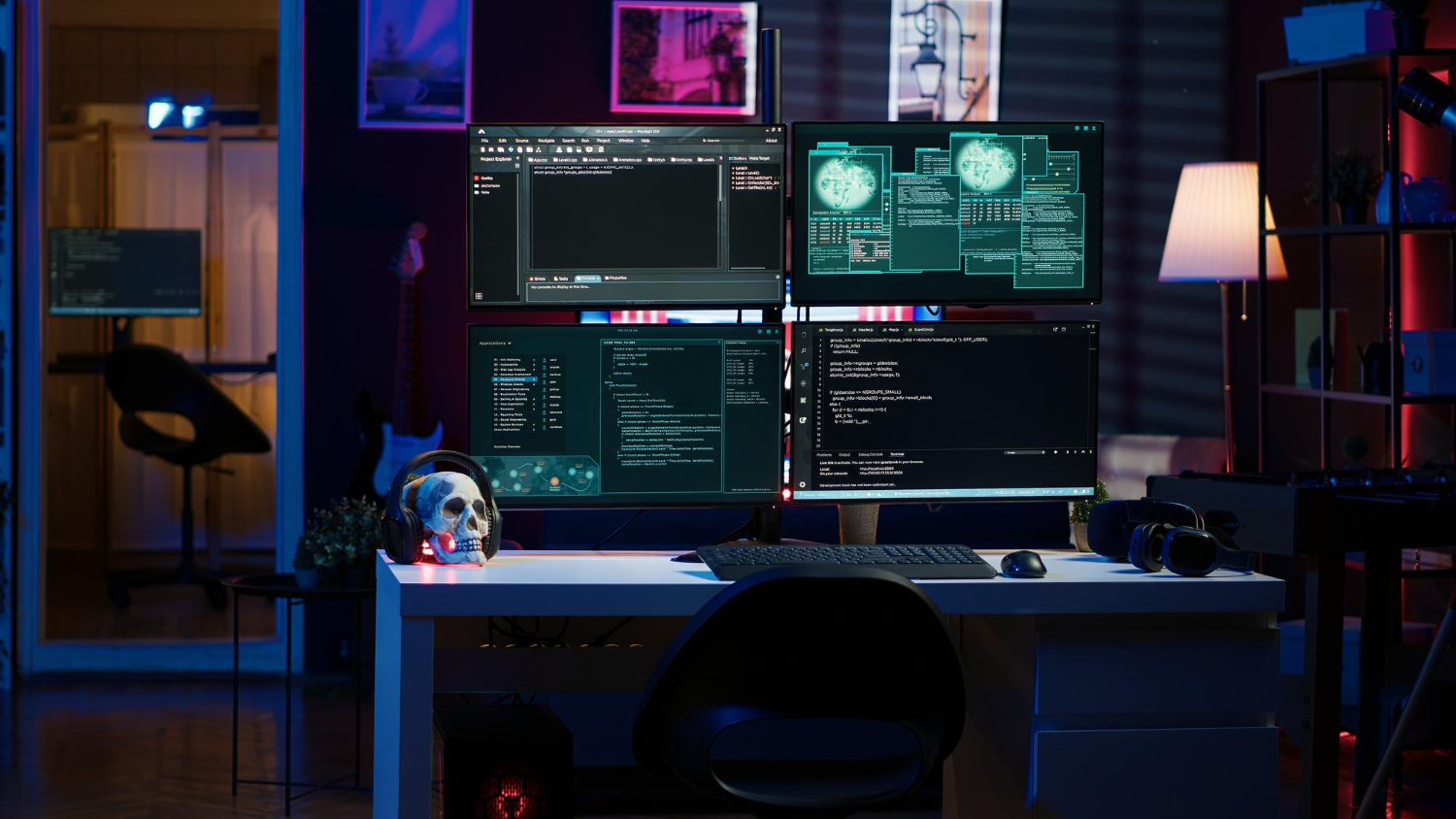
The rise of remote work has transformed the way businesses operate, offering greater flexibility and convenience for employees. However, this shift has also introduced new cybersecurity challenges. With employees accessing company networks and data from various locations, the traditional security perimeter has expanded, leaving businesses more vulnerable to cyber threats. Understanding these risks and implementing strategies to protect your virtual office is critical to safeguarding your business and data.
The New Cybersecurity Landscape of Remote Work
Remote work environments are inherently different from traditional office settings. Employees use personal devices, unsecured Wi-Fi networks, and a mix of cloud-based tools to access company data and applications. While these technologies offer convenience and efficiency, they also create multiple entry points for cybercriminals.
Cybersecurity threats in remote work can range from phishing attacks to data breaches, ransomware, and more. Below are some of the most common threats remote workers face, along with strategies to secure your virtual office.
Common Cybersecurity Threats in Remote Work
- Phishing Attacks Phishing is one of the most common cyber threats remote workers encounter. Cybercriminals use fake emails, phone calls, or text messages to trick employees into revealing sensitive information, such as login credentials or financial details. These attacks are often disguised as legitimate communications from trusted sources.Mitigation Strategy: Implement a robust email filtering system that can detect phishing attempts and block malicious emails. Conduct regular phishing awareness training for employees to help them identify suspicious communications.
- Unsecured Wi-Fi Networks Many remote workers access company resources from public or unsecured Wi-Fi networks, such as those in cafes, airports, or hotel lobbies. These networks are vulnerable to man-in-the-middle attacks, where hackers can intercept communication between a device and the network.Mitigation Strategy: Encourage employees to use Virtual Private Networks (VPNs) when accessing company data remotely. VPNs encrypt internet traffic and provide a secure connection, even on public networks.
- Weak Passwords Weak or reused passwords are a common vulnerability in remote work environments. Employees often use simple passwords or reuse passwords across multiple accounts, making it easier for cybercriminals to gain unauthorized access to company systems.Mitigation Strategy: Enforce strong password policies, requiring employees to use complex, unique passwords for each account. Additionally, implement Multi-Factor Authentication (MFA) to add an extra layer of security to the login process.
- Data Breaches Remote work increases the risk of data breaches, especially if employees store sensitive company information on their personal devices or cloud storage services. A breach can occur if these devices are lost, stolen, or compromised by malware.Mitigation Strategy: Implement endpoint security solutions to monitor and secure all devices accessing company data. Require employees to use company-approved devices and secure cloud storage services. Additionally, enforce encryption for all sensitive data.
- Ransomware Attacks Ransomware attacks have become a significant threat to remote workers. Cybercriminals use ransomware to lock files or entire systems and demand payment for their release. These attacks can have devastating consequences for businesses, particularly if critical systems or data are compromised.Mitigation Strategy: Regularly back up company data to an encrypted cloud storage or external server. Ensure that all systems are updated with the latest security patches, and use antivirus and anti-malware tools to detect and block ransomware before it spreads.
- Lack of Security Awareness Many remote workers may not fully understand the risks they face or the security measures they need to take. A lack of awareness can lead to careless mistakes, such as clicking on malicious links, sharing passwords, or using insecure devices to access company resources.Mitigation Strategy: Conduct regular cybersecurity training sessions to educate employees about common threats, secure online practices, and the importance of maintaining strong security hygiene. Encourage a culture of vigilance to ensure that security is always top of mind.
Best Practices to Secure Your Virtual Office
- Establish a Remote Work Security Policy Create a comprehensive security policy that outlines the procedures and tools employees should use when working remotely. This policy should cover topics like password management, VPN usage, acceptable devices, and data storage practices.
- Implement Endpoint Security Solutions Secure all endpoints—such as laptops, smartphones, and tablets—that access company systems. Use endpoint detection and response (EDR) solutions to monitor for unusual activity, detect threats, and automatically respond to potential security incidents.
- Secure Cloud Services Many remote workers rely on cloud-based applications for collaboration and file sharing. Ensure that these services have strong security features, such as encryption, MFA, and access controls. Regularly review and update your cloud security policies to minimize risks.
- Regularly Update Software and Systems Software vulnerabilities are often exploited by cybercriminals. Ensure that all devices and applications used for remote work are regularly updated with the latest security patches and updates.
- Monitor and Audit Access Continuously monitor who has access to company resources, and regularly audit user activity to detect any suspicious behavior. Limit access to sensitive data based on the principle of least privilege—only give employees access to the data they need for their job.
- Backup Data Regularly Establish a routine for backing up critical company data. Ensure that backups are encrypted and stored in a secure location, either in the cloud or on a physical device. This will help your business recover quickly in the event of a data breach, ransomware attack, or system failure.


Conclusion
Cybersecurity in remote work environments is more critical than ever. As remote work continues to grow in popularity, businesses must take proactive steps to protect their virtual offices from evolving threats. By implementing strong security policies, utilizing the right tools, and educating employees on best practices, you can ensure that your remote workforce is equipped to work securely, no matter where they are. Prioritizing cybersecurity will not only protect sensitive business data but also maintain trust with customers, partners, and stakeholders.